API Gateway vs. Load Balancer vs. Reverse Proxy: The 2026 Architect's Guide
Imagine this: It’s Black Friday. Your e-commerce application is getting hammered with 50,000 requests per second. Suddenly, the authentication service chokes, dragging the entire product catalog down with it. Your monitoring dashboard is a sea of red.
Why? Because you used a simple Load Balancer when you needed an API Gateway to handle rate limiting.
If you’ve ever stared at a whiteboard, marker in hand, wondering, "Do I really need NGINX if I have AWS API Gateway?" or "Can't my Load Balancer handle SSL termination?"—you are not alone. These three components are the "Bermuda Triangle" of system design; they overlap just enough to be confusing, but are distinct enough to crash your system if swapped incorrectly.
In this guide, we’ll dissect the difference between API Gateway, Load Balancer, and Reverse Proxy, exploring their specific roles, how they fit into modern 2026 architectures, and why the rise of AI is changing the rules of the game.
The "Traffic Cop" vs. "The Bodyguard" vs. "The Manager"
Before we dive into the code and configs, let’s simplify the mental model.
1. The Load Balancer (The Traffic Cop) 👮
Goal: Availability & Scalability.
Think of a Load Balancer (LB) as a traffic cop at a busy intersection. He doesn't care who is driving the car or what is in the trunk. His only job is to ensure that no single lane gets clogged while others are empty.
- Function: Distributes incoming network traffic across multiple servers to prevent overload.
- Layer: Operates at Layer 4 (Transport) or Layer 7 (Application).
- Key Feature: Health checks. If Server A dies, the cop stops sending cars that way.
2. The Reverse Proxy (The Bodyguard) 🕶️
Goal: Security & Anonymity.
A Reverse Proxy is like a bodyguard for a celebrity (your server). When a fan (client) wants an autograph, they talk to the bodyguard, not the celebrity. The celebrity never reveals their home address (IP address) to the public.
- Function: Sits in front of one or more servers, intercepting requests to hide backend details.
- Key Feature: Caching and SSL Termination. The bodyguard handles the "handshakes" so the celebrity can focus on their talent.
3. The API Gateway (The Manager) 👩💼
Goal: Management & Rules.
An API Gateway is the celebrity’s manager. The manager doesn’t just block fans; they check if the fan has a VIP pass (Authentication), enforce limits on how many questions they can ask (Rate Limiting), and translate requests (e.g., "She doesn't speak French, speak English").
- Function: A specialized reverse proxy that creates a single entry point for a group of microservices.
- Key Feature: Protocol Translation (e.g., REST to gRPC) and API Composition.
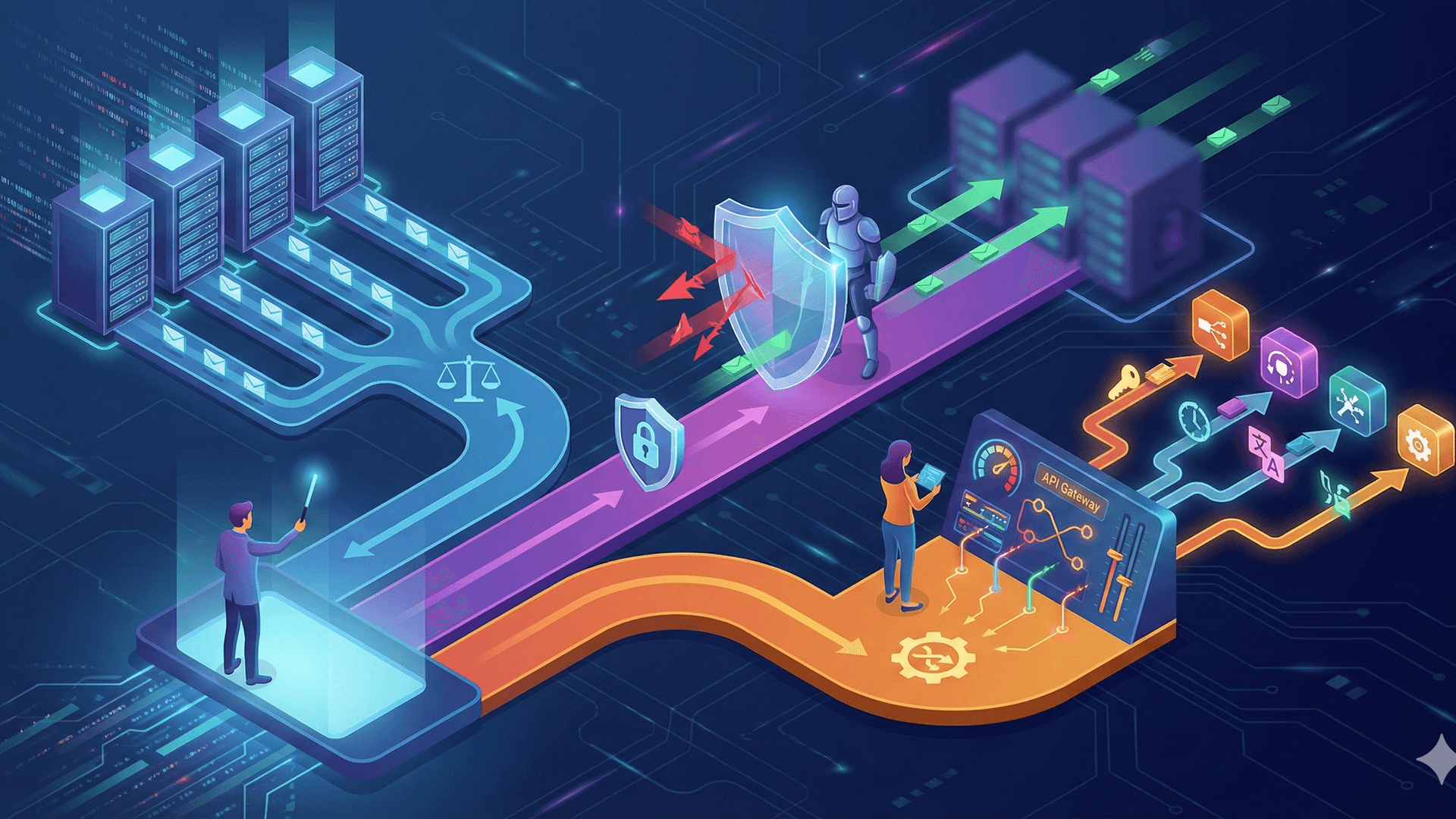
Visualizing the Architecture
To understand how these components stack, let's look at a standard microservices setup.
Have you ever wondered why your "simple" app has 4 layers of network hops? It’s usually because each layer solves a problem the previous one couldn't.
Deep Dive: The Core Differences
Let's break down the technical distinctions that matter in 2026.
1. Scope of Traffic
- Load Balancer: Focuses on volume. It handles massive throughput, ensuring packets get from point A to point B efficiently.
- API Gateway: Focuses on content. It inspects the request body, headers, and tokens. It knows the difference between a
/buyrequest and a/browserequest.
2. Security Capabilities
While all three contribute to security, their roles differ:
| Component | Security Role |
|---|---|
| Reverse Proxy | Hiding Infrastructure. Prevents direct access to backend IPs. Handles DDoS mitigation by absorbing the initial hit. |
| Load Balancer | Resilience. Protects against SYN floods and ensures traffic goes only to healthy instances. |
| API Gateway | Policy Enforcement. Validates JWTs, handles OAuth2 flows, prevents SQL injection via WAF integration, and enforces quotas. |
3. Recent Developments (2025-2026 Trends) 🚀
The landscape has shifted. If you are building today, you need to be aware of these evolutions:
The Rise of the "AI Gateway"
With the explosion of LLMs, we are seeing a new variant: the AI Gateway.
- Prompt Caching: Why pay OpenAI for the same query twice? AI Gateways now cache semantic results.
- Model Routing: The Gateway decides dynamically: "Simple query? Route to Llama-3-8B (Cheap). Complex reasoning? Route to GPT-5 (Expensive)."
- Token Rate Limiting: Traditional gateways limit requests per second. AI Gateways limit tokens per minute to control costs.
eBPF and the Service Mesh
The line between Load Balancers and Sidecars is blurring. Technologies like eBPF (Extended Berkeley Packet Filter) allow us to run high-performance load balancing logic directly in the operating system kernel, bypassing the need for heavy proxy sidecars.
"In 2026, the best load balancer is the one you don't even know is there. eBPF is making network layers invisible." — Senior Architect, CloudNative Corp
When to Use What? (The Decision Logic)
Struggling to decide? Ask yourself these rhetorical questions:
- Do you need to route requests based on the user's subscription tier?
- Yes? You need an API Gateway. A Load Balancer can't read user tiers inside a JWT.
- Are you simply trying to keep your website online while deploying new code?
- Yes? A Load Balancer with "Blue/Green" deployment capabilities is your friend.
- Do you have a legacy system that speaks XML, but your frontend acts like it only knows JSON?
- Yes? Use an API Gateway for request transformation.
Real-World Scenario: The "Super-App"
Let's look at a concrete example of a Super-App like Uber or Grab.
- The Load Balancer (Layer 4): Receives the TCP connection from the user's phone. It ensures the connection goes to an available data center region (e.g.,
us-east-1vseu-central-1). - The Reverse Proxy (Layer 7 - NGINX): Terminates the SSL certificate (decrypts traffic) and compresses the response (gzip/brotli) to save bandwidth. It might cache static images of restaurant menus.
- The API Gateway (Kong/Apigee): Authenticates the user. It sees the request is for
/ride/request. It checks if the user has an outstanding balance. If clear, it routes the request to theRideMatchingService.
Conclusion
The difference between API Gateway, Load Balancer, and Reverse Proxy ultimately comes down to intent.
- Use a Load Balancer to keep the lights on (Availability).
- Use a Reverse Proxy to keep the bad guys out and the data fast (Security/Performance).
- Use an API Gateway to manage the business logic of your traffic (Orchestration/Policy).
In 2026, the lines are blurring. Modern tools like Envoy or Cilium can often do all three. However, separating these concerns logically in your head—and your architecture diagrams—is the hallmark of a senior software architect.
Don't let your architecture be an accident.
References
- RFC 9700 - Best Current Practice for OAuth 2.0 Security
- API Management Trends in 2025 - API7.ai
- Load Balancer vs. Reverse Proxy vs. API Gateway - ByteByteGo
- AI Gateways: The Future Trend of AI Infrastructure
📢 Share the Knowledge
Did this clear up the confusion? Share this article with your engineering team to settle the debate once and for all.